Build daily in-app habits that drive 3–5× retention →
Stop losing revenue to external apps. Own your social graph with Social+ SDK.
You add real-time chat or social features to your app. Users love the instant connection. Yet one data breach or compliance violation can destroy trust overnight.
Real-time chat SDKs handle sensitive conversations. Social feeds store personal interactions. Without ironclad security your users become vulnerable.
This guide delivers actionable best practices for 2026. You will learn how to secure authentication, encryption, data privacy, moderation, and monitoring from day one.
Follow these steps and you protect your users while building features they trust. You avoid costly breaches and regulatory fines that plague unprepared teams.
2026 brings stricter privacy laws and sophisticated attacks. Hackers target chat apps more than ever. Strong security turns your SDK into a competitive advantage.
Developers and product leaders who prioritize these practices reduce breach risk dramatically. Their communities grow faster because users feel safe.
Let’s walk through every layer of protection you need. Start here and future-proof your real-time social infrastructure today.
Real-time chat apps face constant attacks. Man-in-the-middle exploits steal unencrypted messages. API vulnerabilities expose user data at scale.
Phishing inside social feeds tricks users into sharing credentials. Malicious SDKs inject code that leaks conversations. The threats evolve faster than most teams can react.
Privacy regulators fine non-compliant apps millions. Users delete apps after a single breach headline. Security is no longer optional.
According to 2026 industry reports, chat-related data breaches increased 28 percent year-over-year. Social features amplify the attack surface dramatically.
Common risks include weak authentication, insufficient encryption, and poor moderation. Ignoring any one creates a single point of failure.
Secure SDK implementations prevent these issues before they start. You build trust that keeps users engaged long-term.
Explore compliance-focused resources in our learning hub for deeper dives into threat landscapes.
Start with robust user authentication. Use token-based systems with short expiration times. Refresh tokens securely on the client side.
Implement multi-factor authentication for sensitive actions. Role-based access controls limit what each user can see or do inside chat rooms.
Never store raw passwords. Hash and salt credentials on the server. Validate every API call with proper authorization checks.
Secure SDKs should enforce these by default. Avoid exposing admin endpoints in client-side code. Rotate keys regularly to limit damage from leaks.
Monitor login patterns for anomalies. Flag unusual locations or devices instantly. This stops account takeovers before they escalate.
Integrate single sign-on for enterprise apps. It simplifies user experience while maintaining enterprise-grade security standards.
These practices prevent the majority of unauthorized access attempts. They form the foundation of any trusted real-time social experience.
Short-lived JWTs with secure refresh mechanisms prevent session hijacking.
Require second factors for high-risk actions like group admin changes.
Limit permissions so users only access their own conversations and rooms.
Real-time alerts for suspicious login behavior across devices.
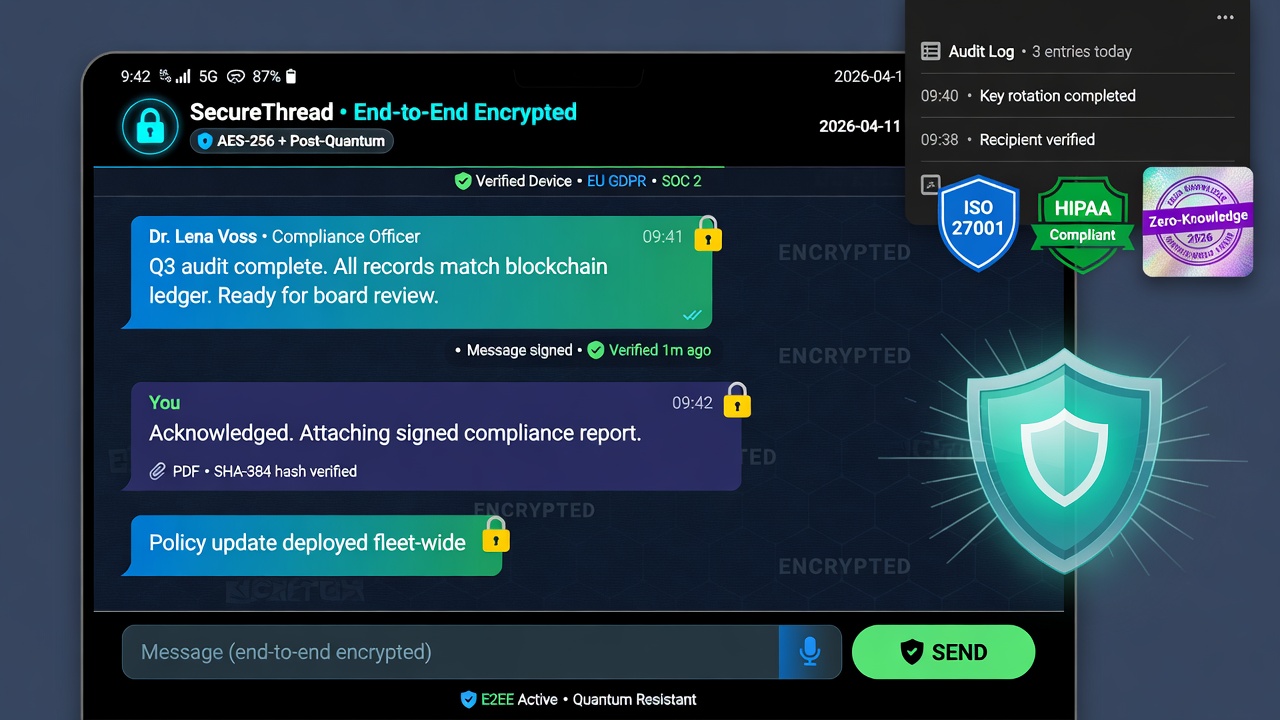
Encrypt all data in transit using TLS 1.3 or higher. This protects messages from network eavesdroppers during transmission.
Go further with end-to-end encryption for private chats. Only the sender and recipient hold decryption keys. Servers never see plaintext content.
Encrypt data at rest in your databases and caches. Use strong algorithms like AES-256 with proper key management.
Secure file attachments and media shares with the same standards. Scan uploads for malware before storage or delivery.
Implement perfect forward secrecy so past sessions remain secure even if long-term keys are compromised later.
SDK providers should offer built-in encryption libraries that developers can enable with minimal configuration. Test thoroughly in staging environments.
These layers ensure conversations stay private. Users trust your app with their most sensitive discussions.
Comply with GDPR for EU users. Obtain explicit consent before collecting personal data. Provide easy ways to delete conversations on request.
Follow COPPA rules for apps targeting children under 13. Get verifiable parental consent before any data collection or social features activate.
Implement data minimization. Collect only what you need for chat functionality. Delete old messages automatically after user-defined retention periods.
Offer data export tools so users can download their chat history. Document every processing activity for audit readiness.
Appoint a data protection officer if your user base exceeds certain thresholds. Train your team on privacy-by-design principles from the start.
These steps avoid massive fines and build user confidence. Privacy-first design becomes a selling point in 2026.
Learn more about compliance in different sectors on our industries page.
Check detailed GDPR guidance for mobile apps at SecurePrivacy’s 2026 Guide.
Implement real-time moderation for public rooms and feeds. Use AI combined with human review to catch harmful content quickly.
Allow users to report messages or users with one tap. Route reports to a dedicated moderation dashboard for fast action.
Apply rate limiting to prevent spam or abuse. Block suspicious IP ranges or device fingerprints automatically.
Support user-controlled privacy settings. Let individuals mute, block, or leave groups without admin intervention.
Log moderation actions for transparency and legal protection. Anonymize logs where possible to respect user privacy.
These tools keep communities welcoming and safe. They reduce legal risk while encouraging positive interactions.
Hybrid moderation catches toxicity faster than either alone.
Users flag issues instantly for rapid response.
Prevents spam and coordinated abuse attacks.
Empower individuals to manage their own experience.
Validate every input on the server side. Sanitize messages to prevent injection attacks like XSS or SQL injection.
Use secure coding practices throughout your SDK. Avoid logging sensitive data in production environments.
Implement rate limiting and throttling on all endpoints. This stops brute-force or DDoS attempts against chat services.
Regularly scan dependencies for known vulnerabilities. Update SDK versions promptly when security patches release.
Sign your SDK releases and verify integrity during installation. This prevents tampering in the supply chain.
Provide clear documentation on secure configuration options. Developers should never need to disable safety features.
These hardening steps protect against common developer mistakes and external attacks alike.
Monitor all chat traffic for anomalies in real time. Set alerts for unusual message volumes or patterns.
Centralize logs without storing plaintext content. Use structured logging for easy searching during investigations.
Develop a clear incident response plan specific to chat breaches. Test it quarterly with simulated attacks.
Notify affected users quickly and transparently when incidents occur. Provide guidance on next steps.
Conduct regular security audits and penetration tests. Engage third-party experts to find blind spots.
These practices minimize damage when issues arise. They demonstrate your commitment to user safety.
Step 1: Choose SDKs with built-in security features. Verify they support E2EE and compliance standards out of the box.
Step 2: Set up proper authentication flows before enabling any chat functionality. Test thoroughly with edge cases.
Step 3: Enable encryption layers one at a time. Start with transit, then add end-to-end and at-rest protection.
Step 4: Configure moderation tools and user controls immediately after launch. Train moderators on your policies.
Step 5: Integrate monitoring and logging from day one. Set up alerts for critical security events.
Step 6: Document your security configuration. Share it with your team and auditors for ongoing compliance.
Step 7: Schedule regular reviews and updates. Security is never a one-time task.
Follow this checklist and you launch with confidence. Your users stay protected as your community grows.
Fintech apps secure trading rooms with strict E2EE and audit logs. Users discuss sensitive market moves safely.
Gaming communities use role-based access to protect voice channels from harassment. Moderation keeps tournaments fair.
Healthcare platforms comply with HIPAA while enabling patient support chats. Encryption protects medical discussions.
Education apps enforce COPPA rules for student rooms. Parental controls give families peace of mind.
Each vertical adapts the same core practices to unique needs. The result is trusted social experiences everywhere.
Discover more sector-specific security tips on finance and healthcare pages.
Review your current setup against these standards. Prioritize gaps that expose user data first.
Automate security checks in your CI/CD pipeline. Catch issues before they reach production.
Train developers on secure SDK usage. Make security part of every code review.
Stay updated on new threats through industry reports and security bulletins.
These habits keep your real-time chat and social features safe for years ahead.
Prepare for quantum-resistant encryption as computing power advances. Start testing post-quantum algorithms now.
Adopt zero-trust architectures for all social interactions. Verify every request regardless of user status.
Explore decentralized identity solutions for greater user control over personal data.
AI-assisted threat detection will become standard. It spots subtle abuse patterns humans might miss.
Stay ahead by building flexible security layers that adapt without major rewrites.
Use established libraries like Signal Protocol or built-in SDK options. Generate keys client-side and never expose them to servers. Test interoperability across devices thoroughly.
GDPR for data rights, COPPA for younger users, and HIPAA for health-related chats. Always match your app’s audience and features to the right regulations.
Run full audits quarterly plus after any major update. Include penetration testing and dependency scans to catch new vulnerabilities early.
No. Configure secure options, monitor your own traffic, and maintain your incident response plan. Shared responsibility keeps everyone protected.
Security is the foundation of every successful real-time chat and social experience. Implement these best practices from the beginning.
Your users will notice the difference. They stay longer, share more, and recommend your app with confidence.
Start today with a quick security audit of your current SDK setup. Small improvements deliver big protection gains.
Ready to strengthen your real-time social features? Check implementation guides in our developer portal or connect with experts.
Key external resources used: SecurePrivacy 2026 GDPR Guide and Usercentrics COPPA Compliance Hub for the latest regulatory insights.
Stop losing revenue to external apps. Own your social graph with Social+ SDK.
Guilds, leaderboards and watch parties
Portfolio sharing, group investing and live trading rooms
Study groups, peer leaderboards and live classrooms
Group trip planning and real-time shared experiences
Live shopping, group buys and influencer feeds
Challenges, kudos and community workout streaks
Fan communities, fantasy leagues and live match chats
Secure care-team chat, patient support circles and family hubs
Live voice rooms, creator AMAs and podcast communities